At a meeting on a completely different subject, I was interviewed
about
SpamRankings.net.
Here's
the audio,
and here's the blurb they supplied:
At a meeting on a completely different subject, I was interviewed
about
SpamRankings.net.
Here's
the audio,
and here's the blurb they supplied:
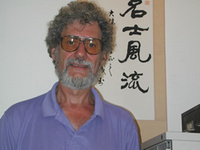
John S. Quarterman, long time Internet denizen, wrote one of the
seminal books about networking prior to the commercialization of the Internet. He co-founded the first Internet consulting firm in Texas (TIC) in 1986, and co-founded one of the first ISPs in Austin (Zilker Internet Park, since sold to Jump Point). He was a founder of TISPA, the Texas ISP Association. Quarterman was born and raised in Lowndes County, where he married his wife Gretchen. They live on the same land where he grew up, and participate in local community and government.
Quarterman took some time during Georgia River Network's Weekend for Rivers to speak with the Nonprofit Snapshot about spam-mapping and small town politics.
More about Elinor Ostrom's Nobel-prize-winning work on organizing the commons, and how that applies to SpamRankings.net.
The water organization has since been incorporated as the Georgia non-profit WWALS Watershed Coalition:
WWALS is an advocacy organization working for watershed conservation of the Willacoochee, Withlacoochee, Alapaha, and Little River Systems watershed in south Georgia and north Florida through awareness, environmental monitoring, and citizen advocacy.
-jsq