How to do a ranking when you can’t present a rank list:
use a distribution graph.
Also how to do a randomized control trial when there are active
enemy agents:
five ways to find out if and how much they are affecting the results.
This was in my apparently annual talk at TPRC 41, the Telecommunications
Policy Research Conference in Arlington, Virginia.
How to do a ranking when you can’t present a rank list:
use a distribution graph.
Also how to do a randomized control trial when there are active
enemy agents:
five ways to find out if and how much they are affecting the results.
This was in my apparently annual talk at TPRC 41, the Telecommunications
Policy Research Conference in Arlington, Virginia.
With slides, abstract, full paper, and video.
The sound is not good, though; it was taken with my smartphone.
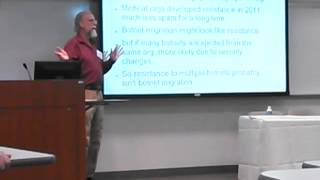 Why don’t conferences do their own video and put it on the web?
There were a few sensitive presentations at this one, but they
were few, and the rest could have gone up.
They didn’t, so I got somebody to video with my phone.
Why don’t conferences do their own video and put it on the web?
There were a few sensitive presentations at this one, but they
were few, and the rest could have gone up.
They didn’t, so I got somebody to video with my phone.
-jsq

 US
US IN
IN CN
CN