Remember those
three spamming medical organizations PSBL saw and the spike from CSHS
that SpamRankings.net found in CBL data?
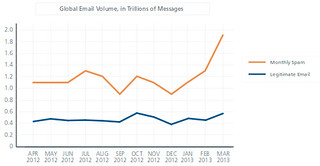
Digging into the underlying data, and graphing them all on the same chart,
we see this:

Even though the three three-digit-spamming medicos spam oddly coherently,
we don’t find any botnets for them.
This may be because most of that spam was seen by PSBL,
and our botnet assignments come from CBL.
CBL didn’t see any spam from those ASNs, so it didn’t have
anything to assign for botnets.
Maybe they’re infested by the same botnet; maybe not; can’t tell.
But it was CBL that saw that big spam spike for AS 22328 CSHS.
And CBL did assign a botnet to that: Lethic.
For all but two days of CSHS spam shown,
CBL assigned Lethic to the total amount of spam from CSHS for that day.
That may be because all that CSHS spam is coming from a single computer.
Of course, CBL’s botnet assignments are not perfect, but infosec professionals
tell me CBL is about as good as it gets for that, so there’s a good chance
this botnet assignment is correct.
The good news is that all of the trio of three-digit spamming medicos
decreased their spam and even went to zero during the period shown.
And CSHS spam peaked at the end of January and started back down in February.
Pretty soon there may be once again little or no spam from medical organizations
to rank.
-jsq
 McAfee PR of today,
McAfee Quarterly Threat Report Sees Social Media Worm Resurgence as Spam Rises Dramatically:
Targeted Attacks Continue Rise; “Pump and Dump” Returns
with Record Stock Market Highs
McAfee PR of today,
McAfee Quarterly Threat Report Sees Social Media Worm Resurgence as Spam Rises Dramatically:
Targeted Attacks Continue Rise; “Pump and Dump” Returns
with Record Stock Market Highs
















